AN INTELLIGENT FEATURE-OPTIMIZED FRAMEWORK FOR DDoSATTACK DETECTION USING SVM and XGBOOST
DOI:
https://doi.org/10.62050/fjst2026.v10n1.685Keywords:
Distributed Denial of Service (DDoS), Network Intrusion Detection Systems (NIDS), Machine Learning (ML), XGBoost algorithm, Fisher score algorithmAbstract
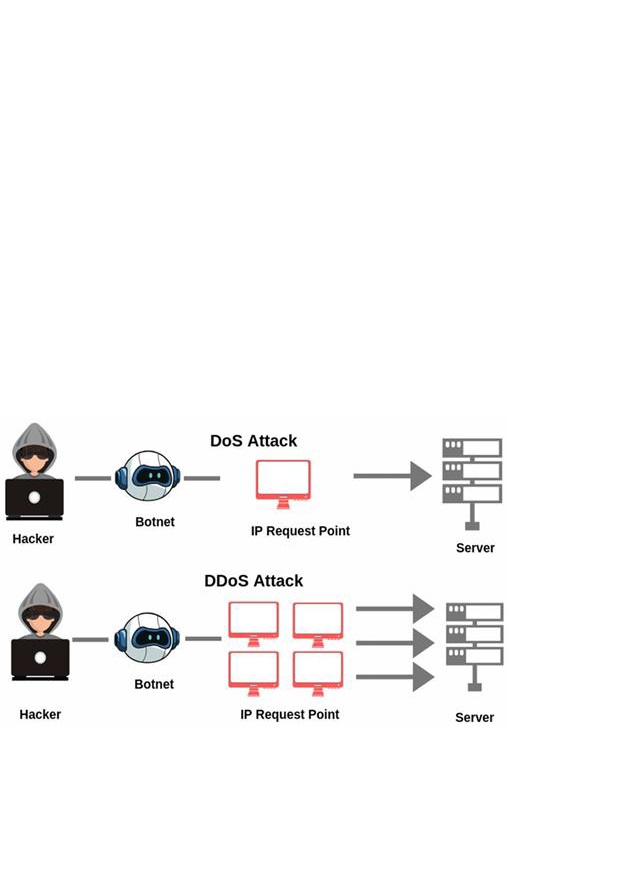
Distributed Denial of Service (DDoS) attacks remain a serious issue for network security, especially within cloud systems that rely on shared and scalable resources. In such settings, attackers can easily use large groups of compromised devices to flood targets with traffic, making genuine access almost impossible. Traditional intrusion detection systems (IDS) that rely on fixed signatures or manually defined rules often fail to keep up, since new and fast-changing attacks rarely fit known patterns. To improve detection, this research applied a machine learning–based approach that combines Support Vector Machine (SVM) and Extreme Gradient Boosting (XGBoost) models, supported by the Fisher Score Algorithm (FSA) for feature selection. The well-known CIC-DDoS2019 dataset from Kaggle was used because it includes both modern DDoS attacks and regular network traffic, giving a practical base for testing the models. Our workflow followed three stages: first, cleaning and preparing the data; second, selecting key features using FSA; and finally, training and evaluating the classifiers. We measured performance with accuracy, precision, recall, F1-score, and the Area Under the Curve (AUC). XGBoost achieved the highest results of 97 % accuracy and an AUC of 0.99, while SVM‟s accuracy fell to 65 % after feature reduction, despite a small AUC gain to 0.65. The results of this study demonstrate that combining machine learning models of XGBoost with FSA significantly improves the detection of DDoS attacks in cloud environments. This highlights its potential for superior performance over traditional IDS methods.
Downloads
References
Ajagbe, S. A., Awotunde, J. B. and Florez, H. (2024). Intrusion Detection: A Comparison Study of Machine Learning Models Using Unbalanced Dataset. SN Computer Science, 5(8), 1028. https://doi.org/10.1007/s42979-024-03369-0
Alhasawi, Y. and Alghamdi, S. (2024). Federated Learning for Decentralized DDoS Attack Detection in IoT Networks. IEEE Access, 12, 42357–42368. https://doi.org/10.1109/ACCESS.2024.3378727
AlSaleh, I., Al-Samawi, A. and Nissirat, L. (2024). Novel machine learning approach for DDoS cloud detection: Bayesian-based CNN and data fusion enhancements. Sensors, 24(5), 1418. https://doi.org/10.3390/s24051418
Altulaihan, E., Almaiah, M. A. and Aljughaiman, A. (2024). Anomaly detection IDS for detecting DoS attacks in IoT networks based on machine learning algorithms. Sensors, 24(2), 713. https://doi.org/10.3390/s24020713
Asaju, La‟aro Bolaji, Peter Bamidele Shola, Nwadike Franklin, and Hambali Moshood Abiola. (2017). Intrusion detection system on a computer network using an ensemble of randomizable filtered classifier. K-Nearest Neighbor Algorithm, 2, 550–553.
Baghdad, Iraq, Abdulrahman, N. F. and Jit Singh, M. S. (2025). Deep learning approaches for DDoS attack detection in communication networks and IoT: A comprehensive review. Journal Kejuruteraan, 37(1), 323–333. https://doi.org/10.17576/jkukm-2025-37(1)-22
Berbiche, N. and El Alami, J. (2024). For robust DDoS attack detection by IDS: Smart feature selection and data imbalance management strategies. Ingénierie Des Systèmes d Information, 29(4). https://doi.org/10.18280/isi.290401
Berhanu, B. and Assamnew, F. (2024). Application Layer Ddos Attack Classification Using Deep Learning. https://doi.org/10.2139/ssrn.4687852
Brown, E., Fisher, J., Hudon, A., Colston, E. and Lu, W. (2024). Multiclassification analysis of volumetric, protocol, and application layer DDoS attacks. In L. Barolli (Ed.), Advanced Information Networking and Applications (Vol. 204, pp. 401–413). Springer Nature Switzerland. https://doi.org/10.1007/978-3-031-57942-4_39
Hadeel S. Obaid and Esamaddin H. Abeed (2020). DoS and DDoS Attacks at OSI Layers. https://doi.org/10.5281/ZENODO.3610833
Hambali, Moshood Abiola and Oforjetu Chukwudi Peter (2024). An Android Malware Detection System Based on Hybrid Artificial Neural Network and Decision Tree Algori., 8(2), 45-68.
Jawahar, A, J., Kaythry, P, Vinoth Kumar, C, Vinu, R., Amrish, Bavapriyan, K. and Gopinaath, V. (2024). DDoS mitigation using blockchain and machine learning techniques. Multimedia Tools and Applications, 83(21), 60265–60278. https://doi.org/10.1007/s11042-023-18028-4
Khan, S. A., Hussain, S. I. and Iqbal, J. (2025). From Signatures to AI: A Comprehensive Review of DDoS Detection Strategies in IoT & SDN. Int. J. on Robotics, Automation and Sciences, 7(1), 19–26. https://doi.org/10.33093/ijoras.2025.7.1.3
Li, J., Luo, T., Zhang, B., Chen, M. and Zhou, J. (2024). IMOABC: An efficient multi-objective filter–wrapper hybrid approach for high-dimensional feature selection. J. of King Saud University - Computer and Information Sci., 36(9), 102205. https://doi.org/10.1016/j.jksuci.2024.102205
Mahboubi, A., Luong, K., Aboutorab, H., Bui, H. T., Camtepe, S., Ansari, K. and Barry, B. (2025). The evolving threat landscape of botnets: Comprehensive analysis of detection techniques in the age of artificial intelligence. Internet of Things, 33, 101728. https://doi.org/10.1016/j.iot.2025.101728
Merkebaiuly, M. (2024). Overview of distributed denial of service (DDoS) attack types and mitigation methods. Inter. Conf., 43(193), 494–508. https://doi.org/10.51582/interconf.19-20.03.2024.048
Pakmehr, A., Aßmuth, A., Taheri, N. and Ghaffari, A. (2024). DDoS attack detection techniques in IoT networks: A survey. Cluster Computing, 27(10), 14637–14668. https://doi.org/10.1007/s10586-024-04662-6
Pang, G., Shen, C., Jin, H. and Van Den Hengel, A. (2023). Deep weakly-supervised anomaly detection. Proceedings of the 29th ACM SIGKDD Conference on Knowledge Discovery and Data Mining, 1795–1807. https://doi.org/10.1145/3580305.3599302
Patel, M., Amritha, P. P., Sudheer, V. B., & Sethumadhavan, M. (2024). DDoS attack detection model using machine learning algorithm in next generation firewall. Procedia Computer Science, 233, 175–183. https://doi.org/10.1016/j.procs.2024.03.207
Ramakrishnan, K., Lutui, R. and Vaipulu, T. (2025). Enhancing cyberattack detection using machine learning techniques in intrusion detection systems. 2025 IEEE 35th International Telecommunication Networks and Applications Conference (ITNAC), pp. 1–8. https://doi.org/10.1109/ITNAC66378.2025.11302561
Raza, M. S., Sheikh, M. N. A., Hwang, I.-S. and Ab-Rahman, M. S. (2024). Feature-selection-based DDoS attack detection using AI algorithms. Telecom, 5(2), 333–346. https://doi.org/10.3390/telecom5020017
Sambangi, S. and Gondi, L. (2020). A machine learning approach for DDoS (distributed denial of service) attack detection using multiple linear regression. The 14th International Conference on Interdisciplinarity in Engineering— INTER-ENG, 51. https://doi.org/10.3390/proceedings2020063051
Santos-Neto, M. J., Bordim, J. L., Alchieri, E. A. P. and Ishikawa, E. (2024). DDoS attack detection in SDN: Enhancing entropy-based detection with machine learning. Concurrency and Computation: Practice and Experience, 36(11), e8021. https://doi.org/10.1002/cpe.8021
Setia, H., Chhabra, A., Singh, S. K., Kumar, S., Sharma, S., Arya, V., Gupta, B. B. and Wu, J. (2024). Securing the road ahead: Machine learning-driven DDoS attack detection in VANET cloud environments. Cyber Sec. and Applic, 2, 100037. https://doi.org/10.1016/j.csa.2024.100037
Setitra, M. A., Fan, M., Benkhaddra, I. and Bensalem, Z. E. A. (2024). DoS/DDoS attacks in software defined networks: Current situation, challenges and future directions. Comp. Comm., 222, 77–96. https://doi.org/10.1016/j.comcom.2024.04.035
Songa, A. V. and Karri, G. R. (2024). An integrated SDN framework for early detection of DDoS attacks in cloud computing. Journal of Cloud Computing, 13(1), 64. https://doi.org/10.1186/s13677-024-00625-9
Uddin, R., Kumar, S. A. P. and Chamola, V. (2024). Denial of service attacks in edge computing layers: Taxonomy, vulnerabilities, threats and solutions. Ad Hoc Networks, 152, 103322. https://doi.org/10.1016/j.adhoc.2023.103322
Xie, B., Wang, Y., Wen, G. and Xu, X. (2023). Application-layer DDoS attack detection using explicit duration recurrent network‐based application‐layer protocol communication models. Int. J. of Intelligent Systems, 1, 2632678. https://doi.org/10.1155/2023/2632678
Xu, K., Li, Z., Liang, N., Kong, F., Lei, S., Wang, S., Paul, A. and Wu, Z. (2024). Research on multi-layer defense against DDoS attacks in intelligent distribution networks. Electronics, 13(18), 3583. https://doi.org/10.3390/electronics13183583